The Distinction That Changes Everything Most discussions of AI and cybersecurity collapse two fundamentally different questions into one. Separating them is not a matter of semantics — it determines what you defend, how you defend it, and who is responsible. Cybersecurity In AI asks: how do we secure the AI system itself? Cybersecurity For AI… Continue reading Cybersecurity In AI and For AI: A Unified Risk Framework from IBM, OWASP, MITRE ATLAS, MIT, and NIST
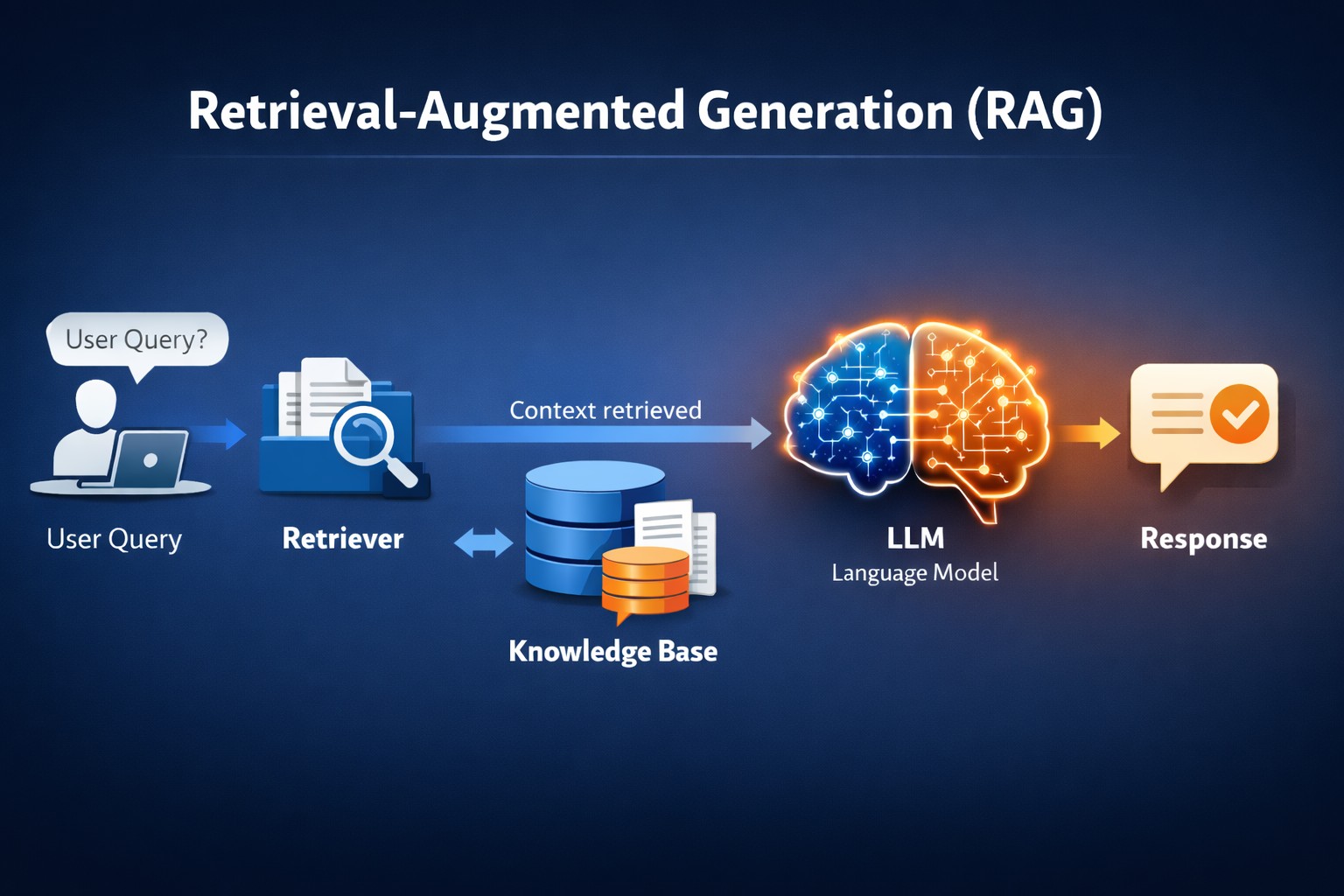
Retrieval-Augmented Generation (RAG)
Retrieval-augmented generation (RAG) is a hybrid AI approach that combines retrieval-based methods with generative models to improve the quality and accuracy of generated content. This approach benefits tasks requiring factual accuracy and natural language generation, such as question-answering, summarization, or generating content based on specific knowledge. How RAG Works: RAG integrates two core components: Retrieval… Continue reading Retrieval-Augmented Generation (RAG)
Cues from OMB Zero Trust Architecture memo
Towards the end of January 2022, the Office of Management and Budget (OMB) released its memorandum on moving government agencies to a zero-trust model. Enterprises that align themselves to industries regulated by the federal agencies can take a cue from it to improve their security posture. The memo considers the recent ransomware attacks on various… Continue reading Cues from OMB Zero Trust Architecture memo
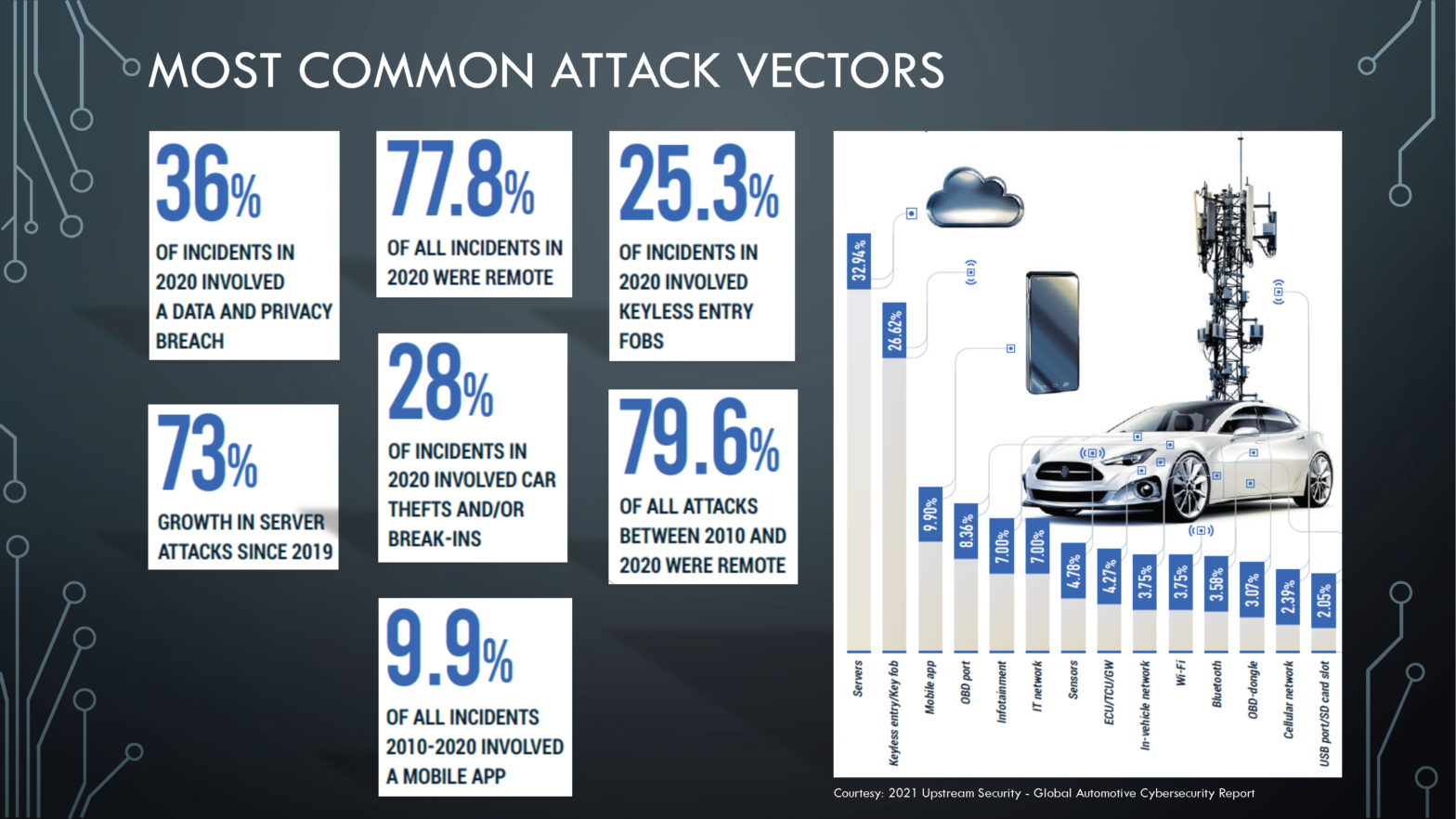
Machine Learning, Society and Cybersecurity
Machine Learning (ML) appears to have made great strides in many areas, including machine translation, autonomous vehicle control, image classification, enabling games on Xbox, PlayStation, Nintendo, and Steam. This has made Artificial Intelligence popular and securing the information in it is challenging. Let’s take a look at an industry that many of us use. We… Continue reading Machine Learning, Society and Cybersecurity
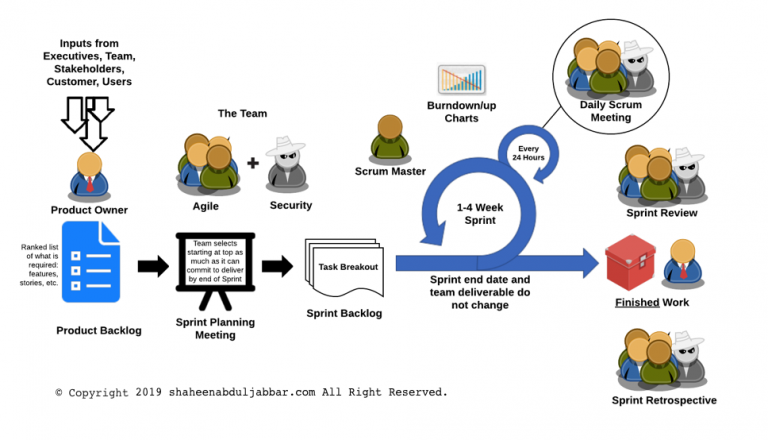
Security in Agile Methodology
Many large organizations are moving towards the Agile software development lifecycle (SDLC) methodology. Agile methodology is a combination of iterative and incremental process models with a focus on process adaptability and customer satisfaction by rapid delivery of working software product. The general characteristics of any Agile methodology are: Prioritizing feedback. Agile teams rely heavily on the… Continue reading Security in Agile Methodology